The range of youngsters who use the Internet is soaring. Currently extra than 30 million children under the age of 18 use the Internet. That represents almost half of the kids residing inside the United States. 14 million children access the facts dual carriageway from college, which is anticipated to increase to 44 million through 2003. Also, by way of that 12 months, we consider greater college students will access the Internet from the classroom than from home, according to the Consortium of School Networking.

Over the ultimate decade, even as the numbers of folks who use the Internet grew, the Internet and it’s far used for has changed as nicely. It is not a community of scientists and academics. Now, anybody can put up whatever they want on an internet site and have an immediate international audience. While the World Wide Web opens up an international of information, enjoyment, and social interaction to children, it also gives them entry to a few very unfriendly records. Today there are nearly 7 million pornography websites on the internet, and that wide variety increases with the day’s aid. Children unwittingly plug a risk-free word into a seek engine. Now, not simplest does the facts they seek pop up, but regularly, so do porn websites and websites with subjects dedicated to bomb-making, weaponry, playing, and pills. Just like the World Wide Web, if we remember it an entity, does now not recognize the ages of those who surf it, inappropriate electronic mail does no longer understand the age of its addressee, and it suggests up in everyone’s email box. Worst of all, the Internet makes it viable for the worst kind of predator, the pedophile, to creep into our schools and houses.
Organizations ranging from schools and hospitals to church buildings and organizations now rely on the Internet to access information. It additionally provides instantaneous get entry to carriers, suppliers, sales, customer support, and greater. But with the coolest comes a few terrible. Along with all of the crucial data that flows across the internet, additional content is at quality besides the point and, at worst, unlawful. Educators who fail to protect their college students from some of this without problems available material face several issues, inclusive of felony liability (remaining year employees at a public library in Minneapolis filed match with the Equal Employment Opportunity Commission (EEOC) pronouncing that exposure to porn because of purchaser surfing constituted an antagonistic work environment) negative publicity, wasted money due to nonproductive use of gadget (extra traces, routers, disk storage, and printers, unreliable or slow connections, and so forth.), and, of the path, the human charges, that are incalculable.
Our kids are our most precious and inclined citizens, and they’re a threat. But the danger is not always in which we as mother and father and educators think it is. Law enforcement officers who deal with the developing problem of cybercrime document that web content is one problem, but fundamental crook interest is taking the region in chat rooms, instant messaging applications, and electronic mail. These modes of conversation have given predators, or pedophiles get admission to online playgrounds in which they find children to absolutely and doubtlessly actually molest. The Internet has furnished these criminals with a means of communicating with thousands and thousands of children. They have an anonymity manner that they may be free to pose as every person they want to.
The problem is bigger than we assume. Consider that one Midwestern city with a populace of one hundred ninety,000 has 270 registered intercourse offenders. This is one small town. When a cybercrime enforcement agent in that metropolis recently logged into a chat room posing as a 13-12 months-old woman, he had ten guys wanting to talk sexually together with her within five minutes!
I. An Overview of the Children’s Internet Protection Act

The Children’s Internet Protection Act was changed into signed into law in December of 2000. The law became effective in April of the remaining yr. CIPA mandates blocking, filtering, or monitoring the era on computer systems in public libraries and colleges receiving E-price telecom reductions or Library Services and Technology Act (LSTA) or Elementary and Secondary Education Act (ESEA) finances to clear out dangerous to minors cloth. The regulation has not been universally praised. Organizations starting from the American Civil Liberties Union to the American Library Association (ALA) have filed fits to overturn the regulation. The ALA believes the law is unconstitutional because it limits get entry to include facts constitutionally. This is to be had on the Internet at public libraries. The invoice added using Senator John McCain, the Republican from Arizona, requires libraries to adopt suited use guidelines followed via era that could block get right of entry to cloth harmful to minors.
This is obviously completely controversial trouble. At one current listening to approximately the Child Online Protection Act (COPA), a hearing that occurred in California, one ALA consultant testified that ALA members routinely overview books and other material, including movies, tune, and magazines, a good way to decide which fabric is appropriate for their readers. They basically clear out cloth earlier than it’s far located on library cabinets. And if it’s miles deemed inappropriate, they block it. At this listening to, a COPA commissioner requested why the ALA no longer needs to do the identical factor for facts on the Internet. The only reply from the ALA consultant: the information is exclusive. Different is actually one way to see it!
My question for you is: why ought to records that are to be had on the Internet be a challenge to much less strict manage than books or magazines or music or video? The material published on paper, whether in books or magazines or appears in video form, is scrutinized very carefully. Federal and kingdom laws mandate that minors be prevented from acquiring some of this cloth. Why must facts on the Internet be handled any in another way? Why should we permit our children to get admission to such material because it is one-of-a-kind? We aren’t speaking approximately ebook burning; we’re truly thinking the controls in place for this new and effortlessly reachable records supply.
I trust that CIPA, COPPA, and COPPA, at the side of all the different acts, proposed, or those which are already regulated, have now not long past some distance sufficient. Our kids are not effectively covered. And it is our activity to deal with the problems that affect our children. We have an ethical responsibility to our future generations to protect them. In our society, kids mature faster due to the myriad of instant communications available; unmonitored communication has contributed to the lack of innocence. We need to guard our children, and now not supply the handiest voice in this challenge to folks that accept as true with the proper to free speech is greater vital than protection.
II. A Look at the History of Content Controls
In the mid-Nineteen Nineties, reviews of the bad reviews children had on the Internet commenced making headlines. At the 1994 Fall Comdex assembly, the National Center for Missing and Exploited Children and the Interactive Services Association issued Child Safety at the Information Highway, the primary statement suggesting that dad and mom should display their children net sports. As any parent knows, Do’s and Don’ts lists, without a doubt, do not work. Kids are curious, and whether or not deliberately or by chance, will discover their way to inappropriate material. If we additionally don’t forget that an estimated 5 million new or renamed websites are placed up each week, it’s smooth to recognize why it appears impossible to defend ourselves and our youngsters from potentially unfavorable cloth. Another technique, limiting getting an entry using rating internet content, prevents youngsters from gaining access to harmful content. The way movie theaters save you kids beneath age 17 from buying tickets to R rated films has been ineffectual. Only about one hundred fifty,000 websites, out of the hundreds of thousands and thousands of net sites, have registered to charge themselves.
Several years ago, in reaction to worries from the public, from mother and father, from educators, and law-enforcement officials, Congress and advocacy corporations began to search for approaches that the authorities could manipulate youngsters to get admission to harmful cloth, a movement that culminated inside the Communications Decency Act, a modification to the Telecommunications Act of 1996.
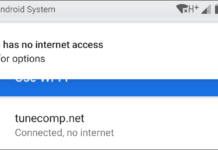
Simultaneously, the rating debate waged, businesses started to develop filtering and tracking software program merchandise. In 1996 there have been just a few; by 1997, there have been about three dozen, and closing yr, there have been greater than a hundred on the market. There is a diffusion of products available. Most depend upon lists of URLs and then block get right of entry to sites that seem to incorporate pornographic fabric. If a person tries to visit this type of site, the person gets a message pointing out that get the right of entry to this precise website is against the law. Other programs filter out the information on the Internet and search for key phrases that indicate the site might also comprise cloth beside the point for kids. The URL blocker blocks the entire website simultaneously as the filter allows admission to the web page but filters out the records besides the point. Opponents say that those processes over block content material, filtering out references to breast most cancers, and to researchers who maintain magna cum laude honors, and so on.

Most lately, several products that display personal activities were provided to the general public. These applications do not block or clear out, but as a substitute, promote the employer Acceptable Use Policy and monitor the pc person activities. If the consumer violates the corporation Acceptable Use Policy by having access to pornographic or different inappropriate fabric, the systems administrator or different assigned person is notified. This method is turning into an increasing number of famous because when an organization posts its Acceptable Use Policy, and its customers recognize their pc use is being monitored, it places the responsibility lower back inside the user’s palms. In different words, if a person knows the Acceptable Use Policy, and he or she chooses to violate the policy, then presumably he or she is willing to suffer the results.